Cyberattacks are costly and disruptive and vulnerabilities are all too common for most organizations. A well-designed Cybersecurity Assessment, carried out on a regular basis, provides organizations with a risk-and fact-based view of the challenges and opportunities associated with cybersecurity and helps address rapidly changing cybersecurity threats and risks. The CSAT is now globally available and exclusively delivered in a Partner-to-Partner model. It helps you to quickly assess an organization’s cybersecurity status and to create a fact-based action plan to improve their cybersecurity. It’s the perfect way to maximize security and to become your customer’s trusted security advisor.
What is CSAT?
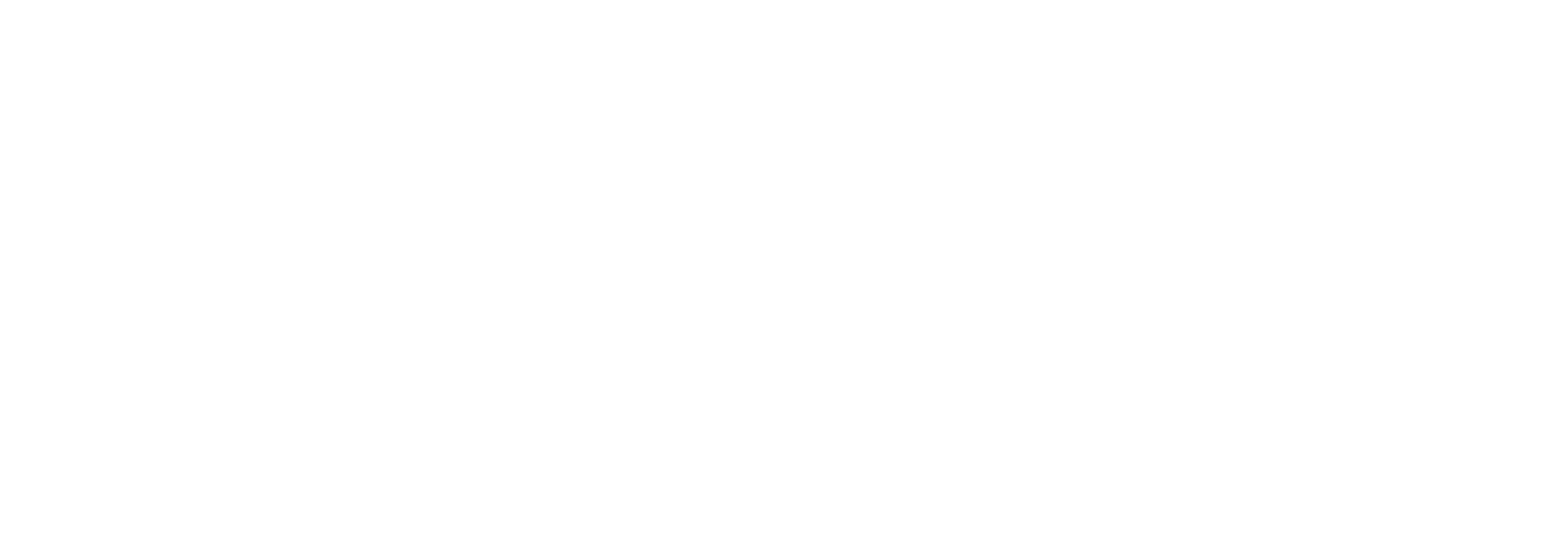
The Cyber Security Assessment Tool (CSAT) is a software product developed by experienced security experts to quickly assess the current status of your organizations security and recommend improvements based on facts. The tool collects relevant security data from the hybrid IT environment by scanning e.g. endpoints, Active Directory and Office 365. Additionally, CSAT uses a questionnaire to collect data about policies and other key indicators.
How does it work?
CSAT is an automated security assessment that provides insights into an organizations security vulnerabilities, based on data from the customer’s infrastructure and Office 365. CSAT collects relevant data by:
- • Scanning endpoints
- • Scanning the Active Directory and Azure AD
- • Scanning content in Office 365, SharePoint, Teams and Intune
By using agents which delete themselves following the endpoint scan, the effort required from the customer’s IT department is kept to a minimum. Information about security processes and procedures is collected through an questionnaire.
Final deliverable
The CSAT delivers a final report containing the customer’s Cybersecurity Maturity Score and a fact- and risk-based action plan. With this report, customers define where to invest their limited security budget and resources and proactively work towards a decent level of security. By periodically assessing the customer’s cybersecurity status, you are proving the measures taken have a positive impact and you proactively discover new improvement areas. It is the perfect way to improve security.










 Contact us
Contact us 





